Indonesia Faces Surge in Cyber Anomalies and Attacks, Data Reveals
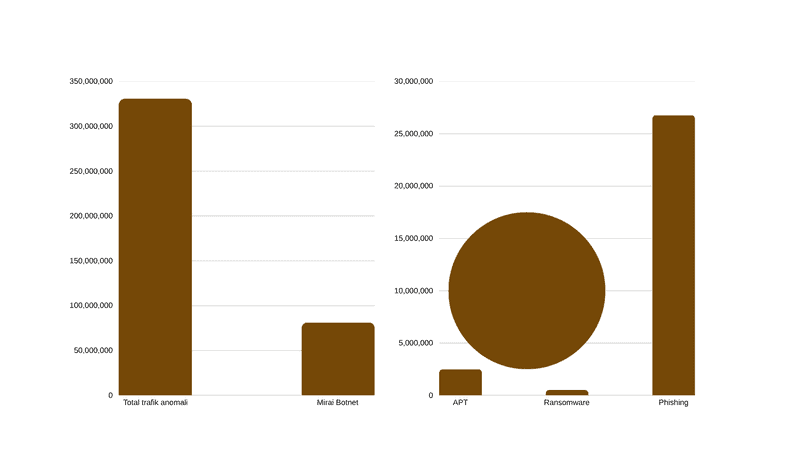
Indonesia experienced a significant wave of cyber activity in 2024, characterized by an overwhelming number of traffic anomalies and specific, targeted threats, according to data from the Indonesia Cyber Security Landscape 2024. This surge underscores the growing vulnerability of national digital infrastructure, a concern highlighted by the recent high-profile attack on the Ministry of Home Affairs. Alarming Traffic Anomalies Dominate Cyber Landscape The total volume of traffic anomalies recorded in Indonesia during 2024 reached a staggering 330,527,636 incidents. The vast majority of this abnormal traffic was attributed to the Mirai Botnet, which alone accounted for 81,286,596 activities. Meanwhile, the country saw millions of specific malicious activities, including: Phishing: The most prevalent attack type, recording 26,771,000 activities. Advanced Persistent Threat (APT): Registered 2,487,041 activities. Ransomware: Recorded 514,508 activities. Critical Incidents and Data Leaks Based on monitoring and Cyber Threat Intelligence results, the National Cyber and Crypto Agency (BSSN) has identified 241 suspected cyber incident leaks. Further darknet investigations uncovered 56,128,160 exposure findings that impacted the data of 461 public interest entities in Indonesia. In cases involving website damage, BSSN recorded 5,780 incidents that targeted several domains and 4,071 incidents specifically targeting online gambling websites. Furthermore, public complaints received by BSSN regarding phishing attacks in 2024 totaled 1,814. The sector grouping of these attacks is based on Presidential Regulation No. 82 of 2022 concerning the Protection of Vital Information Infrastructure (II). High-Profile Attack on Ministry of Home Affairs The severity of the cyber threat was underscored by a direct attack on the official website of the Ministry of Home Affairs (Kemendagri), www.kemendagri.go.id. Service Refusal: Attempts to access the site around 20:40 local time resulted in an error message stating, "This site can't be reached www.kemendagri.go.id refused to connect". Alleged Motive: The then Minister of Home Affairs, Tjahjo Kumolo, confirmed the incident, stating that based on his team's reports, the goal of the hack was allegedly "related to KPK aspirations". Exploited Vulnerability: The security breach was suspected to have been initiated by exploiting a vulnerability within the system, potentially "through the port file transfer and/or through the port database". This incident, alongside the overwhelming statistics on digital anomalies, highlights the pressing challenge Indonesia faces in securing its critical government and public sector digital assets against sophisticated and relentless cyber threats.